[av_textblock size=” font_color=” color=” av-medium-font-size=” av-small-font-size=” av-mini-font-size=” custom_class=” admin_preview_bg=”]
Peer-to-Peer Surveillance Architecture and Automated Camera Response
You may not know that Leverage Detect holds a number of patents. Two of them work together to provide a surveillance system with better detection and response capabilities when compared to more traditional surveillance systems: Peer-to-Peer Surveillance Architecture, and Automated Camera Response.
The patents are architecture-based – that is, how the pieces of a surveillance system work together. This was deliberate, and means we can install whatever hardware we believe best suits in any given environment and requirements, and that hardware will perform exceptionally well within our surveillance architecture.
How do Surveillance Systems work?
Traditional surveillance systems generally provide audio and video monitoring through a hierarchical system. A closed-circuit television system, for instance, can provide video monitoring through a set of closed-circuit cameras that are connected to a single standalone device where the video from the cameras are sent to and viewed. In order for the CCTV surveillance system to operate, there is a single central controller or device that accepts the signals from the closed-circuit cameras, usually via wired connection. This connection presents a single point of failure—if anything happens to the device, the entire surveillance system can fail.
Digital and networked devices were introduced to get around wired connectivity. Digital devices can obviously be set up wirelessly, and they allow for one or more standard network connections that can be used by capture devices, rather than a dedicated video connection. Using the internet, the videos can also be sent through digital networks—something CCTV systems weren’t able to do without great expense.
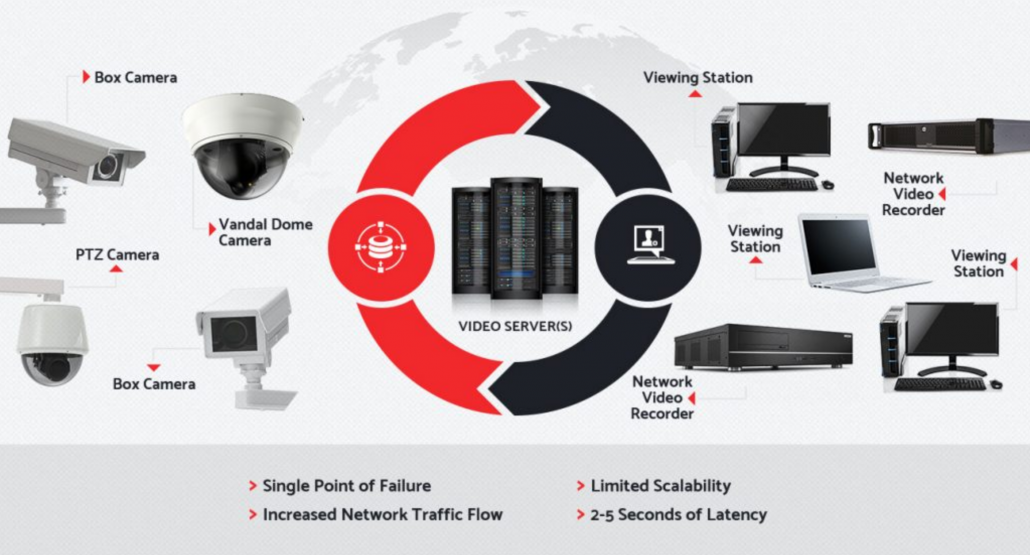 Traditional Client/Server Architecture
Traditional Client/Server Architecture
The digital network-based surveillance systems still continue to rely on a centralized controller in order to function. So even though the problem with wiring CCTV systems has been alleviated by network-based surveillance systems, the single point of failure of the centralized controller still persists in today’s systems. A Peer-to-Peer Surveillance Architecture addresses the deficiency in these systems.
What makes Detect different?
Leverage Detect utilizes a Peer-to-Peer Surveillance Architecture. The surveillance architecture has no central controller because of the independent relationship between its nodes. The nodes of the architecture may refer to capture (camera), viewing, content storage, and so forth. In this sort of structure there are fewer moving parts, which allows for a higher uptime, real-time situational awareness for first responders, and virtually unlimited scalability.
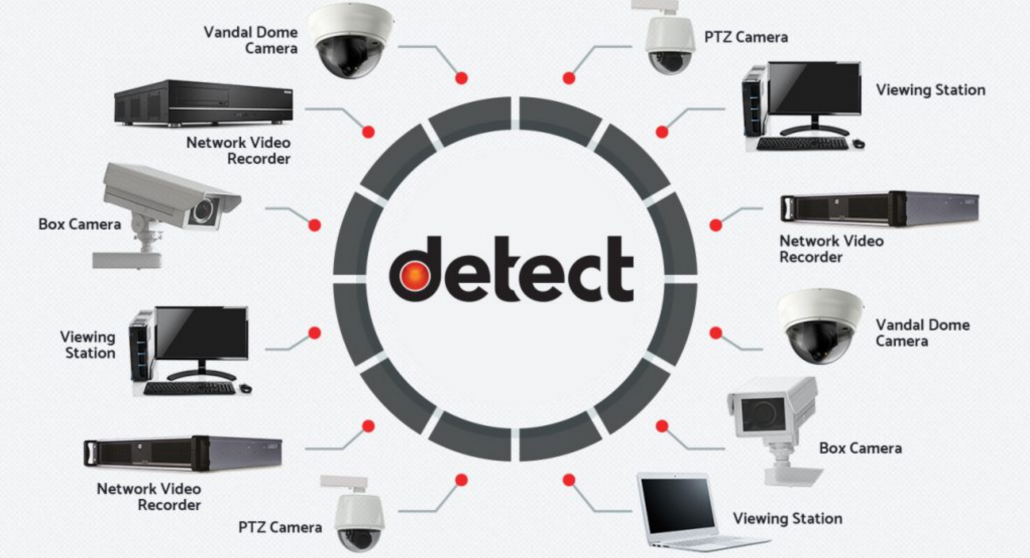
Peer-to-Peer System Architecture
When this type of system is coupled with automated camera response, security, law enforcement, and other first responders have the advantage of immediate eyes on the scene. We call this a “preset response,” and a number of actions can be programmed to respond to likely events or areas of frequent violations.
These actions are programmed and controlled through our Detect VMS software via GeoSpaces—geographic areas on the map interface that have been configured to provoke camera actions automatically, in the reaction to a specific input. Typically, the input would come from a Computer Aided Dispatch (CAD) System, but could also be initiated from a Gun Shot Detect System, License Plate Recognition system, camera notification, or some other detection device.
When an incident occurs within that area, the assigned cameras will action to their predetermined views instantly, providing law enforcement and first responders real-time views. This means a more efficient and appropriate response, and video of the incident will be recorded for later review.
Peer-to Peer Architecture and Automated Camera Response work together seamlessly, making the system more effective than a client-server network.
[/av_textblock]


